 Free Consultation
(610) 667-7511
Free Consultation
(610) 667-7511
 Free Consultation
(610) 667-7511
Free Consultation
(610) 667-7511
 It is no secret that Jennifer Lawrence and quite a few other celebrities had their privacy violated in a horrific way by a hacker or hackers. Their nude photos are plastered across the web, and apparently there are still more to come. The FBI is on the case and chances are good it will identify the people responsible. The last hacker who shared nude photos of an actress (Scarlett Johansson) ended up with a 10 year prison sentence. We can only hope these hackers will be sentenced to an even longer time in prison, given the number of people violated.
It is no secret that Jennifer Lawrence and quite a few other celebrities had their privacy violated in a horrific way by a hacker or hackers. Their nude photos are plastered across the web, and apparently there are still more to come. The FBI is on the case and chances are good it will identify the people responsible. The last hacker who shared nude photos of an actress (Scarlett Johansson) ended up with a 10 year prison sentence. We can only hope these hackers will be sentenced to an even longer time in prison, given the number of people violated.
The issue here isn’t just that pictures were stolen. It is that data on the web is not secure. As a result, it is important that you do everything you can to protect yourself. Whether it is photos, bank data or other private documents, if you have data on the web, you must take certain steps to protect it.
Here are 6 ways you can protect your data.
The first way to protect your data is to have a secure password. A secure password has 12-14 characters and is a mixture of numbers, letters (both upper and lower case) and characters such as @, # and !. Your password should never include a word or number that is easily traced back to you. Do not include your anniversary date or your children’s birthdays. If you cannot think of a password, there are numerous sites that will help you create one. If you must save your passwords somewhere, put it them in an encrypted file and do not write them on a note stored by your computer.
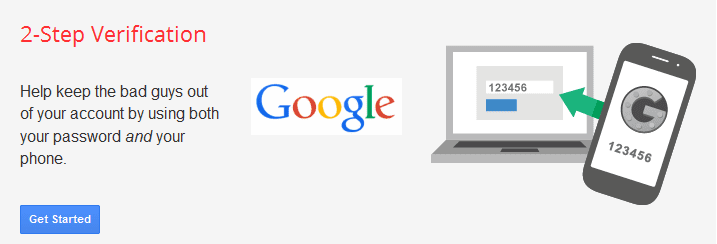
Two step verification is something you should do right now. How it works is that you actually verify the hardware you allow to connect to your accounts ahead of time. If a piece of hardware is not verified, it cannot access your account. Access information about iCloud two step verification on Apple’s website. Instead of recovery questions (which are a common weakness in security) you have a password, authenticated devices and a recovery code. If you lose your code, you will have to prove your identity to Apple to get access to your data again. Two step verification is available for many services. Google offers this level of protection as well.
Every phone and tablet has the ability to add a passcode. Most of the time the passcode is 4 numbers or a pattern. Set this up now. In addition, you can set up your device to wipe if someone keeps trying to log in and fails after a certain number of times.
If you allow Facebook access to your various accounts and Facebook gets hacked, you have lost control of everything. While it is easier to use Facebook to log in, the reality is doing so makes you more vulnerable to having your data stolen.
When you set up an account, you are frequently asked to supply answers to common questions as a way to verify who you are if you forget your password. The problem with this is that many of the questions are too common. If the password question is where were you married, and you publicly write about your anniversary and your wedding on Facebook, then a hacker can guess the answer to that question. Pick unusual questions (if possible) and give nonsensical answers that you can remember.
Encryption protects your data by scrambling it. If someone steals your data and does not have the key necessary to unlock the encryption, he cannot see your data. If the service you are using does not have complete encryption (meaning when it is sitting on the site as well as when it is moving around) you should add encryption. You will have to read up on the service to find out whether it has complete encryption. Unfortunately, encryption will not help you in cases such as the one Jennifer Lawrence experienced, because the hackers likely took advantage of a weakness in iCloud (that Apple has since corrected.) If someone has your password or is able to get into your data storage as if he is you, encryption isn’t going to help. The hacker has the key to unencrypt your data.
Keep in mind, also, that the data is not encrypted on your computer, laptop or phone. Once you download your pictures, if you don’t add encryption on these devices, anyone who can get access to them can steal your data. If you have a USB drive with your data on it, you need to encrypt the drive. That way if it gets stolen or lost, the data will be useless without the key.
Data theft is a serious problem. While many people would condemn Jennifer Lawrence for taking the photos, the reality is she is the victim of a crime. Unfortunately, there are people who would happily steal your data and use it to harm you. The suggestions I have offered can help you protect your private information when you store it on the web.
LOWENTHAL AND ABRAMS, P.C.

Contact us for a FREE consultation. No fee unless compensated.